Empowering Dreams, Building Skills: DICC Institute, Where Careers Take Flight.
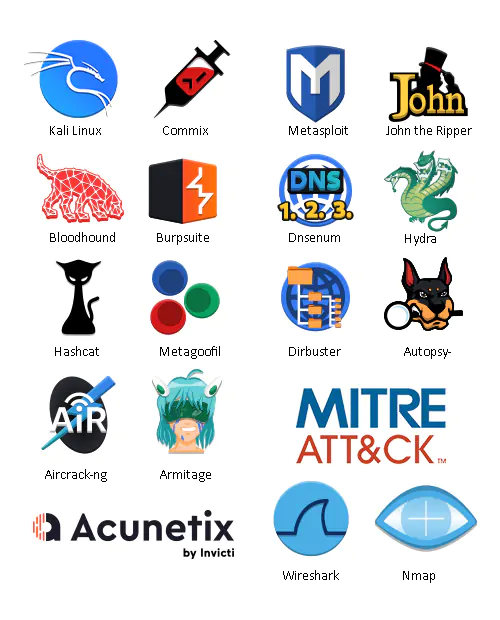
Tools and Languages
We simplified the concepts of ethical hacking to ensure that even students can understand how it works.
Whats Topics Includes?
- OWASP Top 10 Web Application Threat Vectors
- Ransomware/Malware Analysis
- Outdated/Unpatched Software
- System Hacking and Privilege Escalation
- Web Application Hacking and Pen Testing
- Cloud Attack/Hacking
- Social Engineering/Phishing attacks
- Securing the Cloud
- MITRE ATT&CK Framework
- Threat Tactics
- Deep Dive Into the Dark Web
- Firewalls, and Honeypots
- Vulnerability Management
- IoT Attack/Hacking
- Wi-Fi Network Attack/Hacking
- DOS/DDoS Attac
- Mobile Attack/Hacking
- IoT and OT Hacking
- Supply Chain Cyber Attacks
- Cryptography
Course Outline
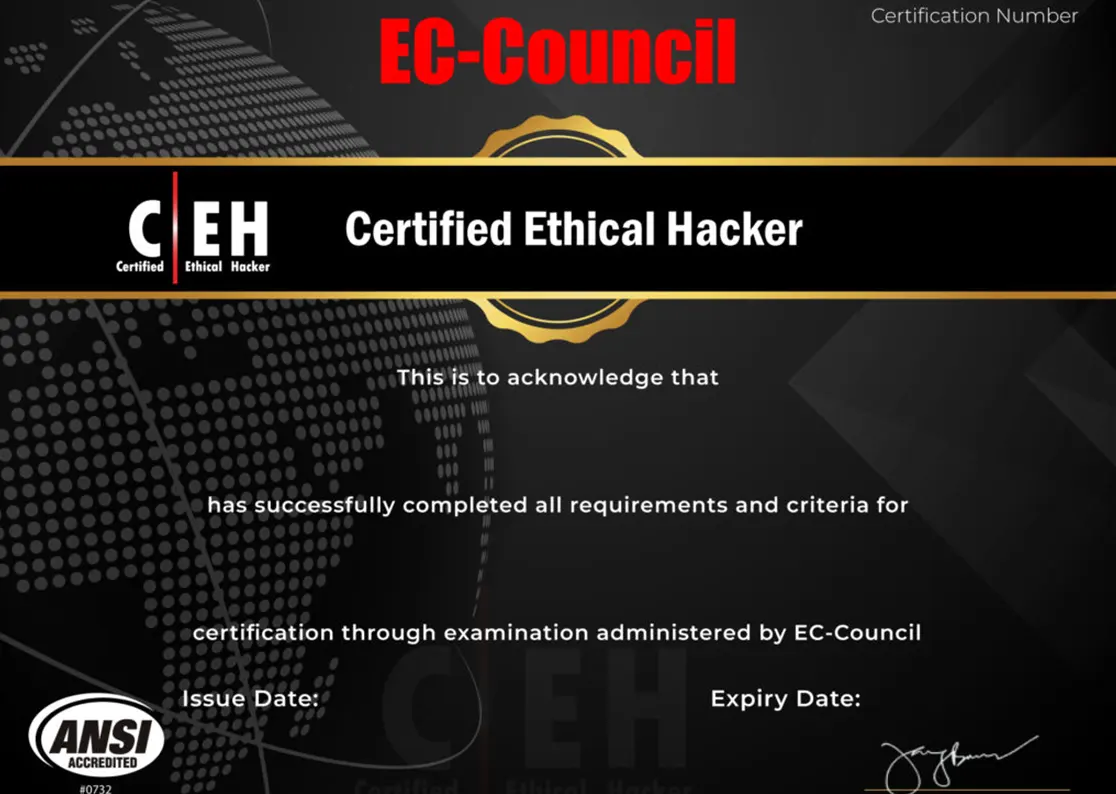
20 Modules: Master Ethical Hacking & Ace the C|EH Certification