Best Hacker Distributions
Gathering your own collection of hacking tools is great, but now it is customary to take as a basis one of the specialized distributions. Usually it is Kali Linux but we will not only look at it but we will also look at other hacking operating systems (pentestest) which are sometimes no less efficient and in some areas more useful.
Operating systems for hacking . Some are popular, others are not very popular, but they all aim to give a hacker a convenient, versatile and reliable tool for all occasions. Most of the programs in such customized assemblies the average hacker will never use, but they are added to the status ponies.
Best operating systems for hacking
Today we will try to make an overview of most interesting distributions for hackers, both popular and undeservedly forgotten. If we missed something, feel free to use the comments. Let’s go!
NST
- First release: 2003
- Based on: Fedora
- Platforms: x64
- Graphic shell: MATE
Let’s start with a little-known, but no less interesting distribution. NST (Network Security Toolkit) is based on Fedora and designed for network attacks. The interface is based on MATE, which makes you feel like you are starting from zero.
The set includes several dozens of the most important tools, mainly network scanners, clients for all kinds of services and all kinds of traffic interceptors. But there is a lack of such useful tools as, for example, masscan, and even the banal aircrack, although airsnort is available.
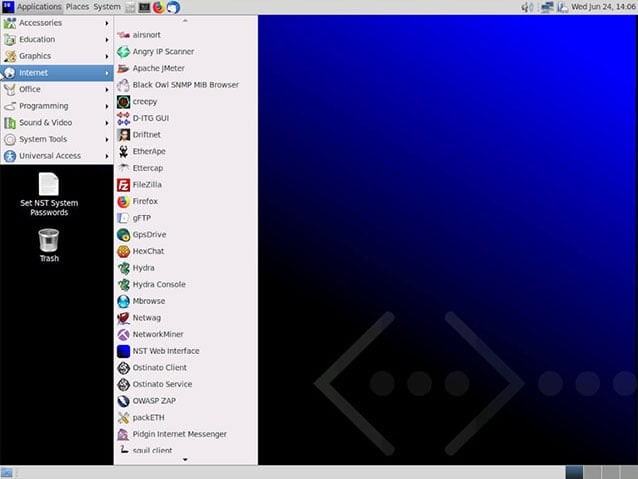
The main part of the tools lies in the Internet folder
The most delicious food can be found in the Applications → Internet folder. Here we have Angry IP Scanner, written in Java, Ettercap and even OWASP ZAP, which we have already written about in the article “Review of the best vulnerability scanners”.
There is a good collection of modules for all sorts of spoofing and scanning in the package. In business, it showed itself quite good, just a pity, not very convenient and terribly outdated.
All the software I have tested works perfectly. In general, everyone who misses the ancient interface and familiar tools is recommended.
Download hacker NST distribution
Kali
- First release: 2013
- Based on: Debian
- Platforms: x86, x64, ARM, VirtualBox
- Graphical front-end: Xfce
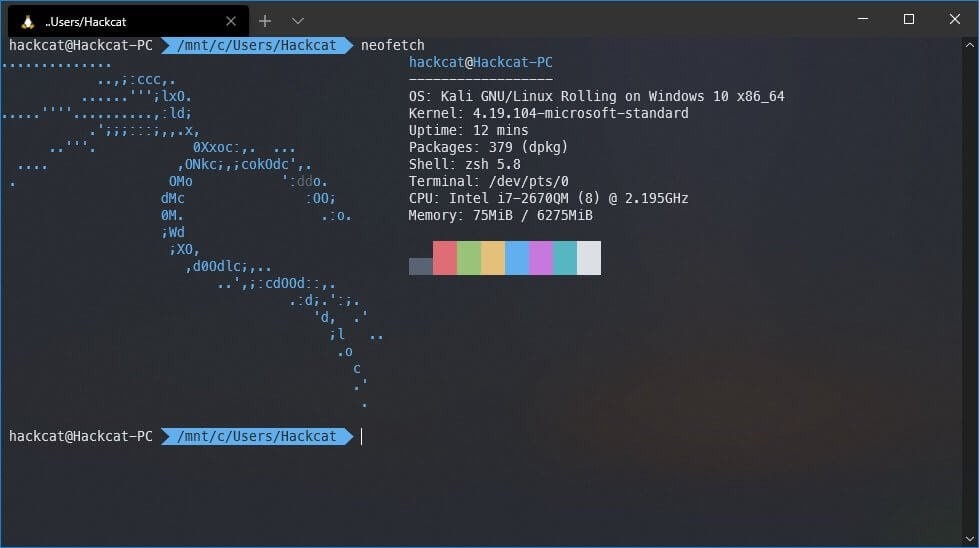
As you obviously know, Kali Linux is one of the most widely distributed distributions for hackers and it would be strange if we did not write about it. Even school children know about it and since relatively recently it is available as an application directly from the Microsoft Store (for more information see “Installing Kali Linux in Windows 10”).
Of course, availability is a definite plus but the system is slightly overloaded with a set of tools (although not as much as BlackArch) and some of them work out of the box curved or do not work at all.
No foolproof protection is provided in Kali either. As practice shows, it is not clear to all users that this system should not be made basic. From the core to the shell, it was designed and optimized for combat missions on the IS fronts and is badly suited for quiet daily work. Many of the mechanisms needed in everyday life are simply absent there, and trying to install them is likely to cause failures in the normal operation of the OS if it does not completely disable it.
In short, Kali is like matches – a powerful thing in capable hands, it is easy to get, but children should not be given. It is not possible to cover all possible official and unofficial utilities (and there are more than 600 of them for a minute) of this system at once, if only because new and new modules, frameworks, utilities and other stuff are constantly appearing.
Kali is designed for a wide range of tasks, but most of them are attacks in the network environment, such as searching for vulnerabilities in web applications and accessing wireless networks. As a successor to BackTrack, Kali is generally well suited to work with wireless communication channels, especially WiFi.
Testing for remote hosts is also possible with Metasploit, for example, but it is WiFi that the core and a large part of the tools are focused on.
Another plus is the large number of dictionaries for various attacks, not only for WiFi, but also for Internet accounts and network services.
For even more convenience, the official website offers a version of the distribution for virtual machines, because when hacked, it is much more reasonable to use the system without installation – not many people will then dig into your computer!
The verdict is as follows: if you know how to use it, it’s a cool thing, but don’t dare show it to your child.
Download the most popular hacker OS Kali Linux
DEFT
- First release: 2005
- Based on: Ubuntu
- Platforms: x86
- Graphic shell: LXDE
Homeland of DEFT is sunny Italy, and it is generous as pizza cheese, sprinkled with a variety of tools for reconnaissance and hacking. At the same time they are not attached to the distribution with blue duct tape, but are quite harmoniously built into it. All together, it resembles an interesting and useful in life Swiss knife.
DEFT was developed on the Lubuntu platform and is equipped with a user-friendly graphical interface. The product includes a set of profile utilities, ranging from antivirus, browser cache search systems, network scanners and other utilities to computer forensics tools that are needed when searching for hidden information on disk.
Using this operating system, it is not difficult to access erased, encrypted or corrupted data on various types of physical media.
The main toolkit is hidden in the DEFT section, which in turn is in some kind of a “Start” menu.
Originally this distribution was designed for the needs of network police and security incident response specialists, so another strong point of DEFT is competitive intelligence, including the analysis of social network account interconnections.
There is even an interesting utility to detect geolocation of a given LinkedIn or Twitter account. I couldn’t check how effective it works at the moment, but it manages to determine if an account belongs to a country and a city.
Unlike Kali Linux, DEFT has a built-in foolproof feature. Without proper training almost no tool can simply not run and without a deep understanding of the security mechanisms there is nothing to do at all.
Literally every application or option requires root permissions so don’t rush to run everything at once or create an unprivileged user.
I also found a “gift”: several repositories from where DEFT takes updates are locked with keys. For a couple of days I searched the forums until I found where to request the data, and the keys themselves were also found.
As a result, this system is good for forensics (computer forensics) and incident investigation, especially if there is physical access to the media – whether it be a disk, flash drive or smartphone (hacker, boss, employee, competitor, wife, mistress – need to emphasize).
Download hacker DEFT distribution
Tsurugi
- First release: 2018
- Based on: Ubuntu
- Platforms: x86 (partially), x64
- Graphic shell: MATE
This distribution is not well known in IB circles at all – perhaps because of its youth. However, Tsurugi is a brainchild born through the joint efforts of the creators of DEFT and Kali. What came out of it? Let’s find out!
Tsurugi (this word means two-handed Japanese sword) is based on Ubuntu, MATE is used as a GUI. It’s more for Forensics or OSINT than for pentest, but its toolkit, like some features, allows it to be used in this direction as well. Initially, the system is supplied in live image mode, but if you want, you can make a permanent installation.
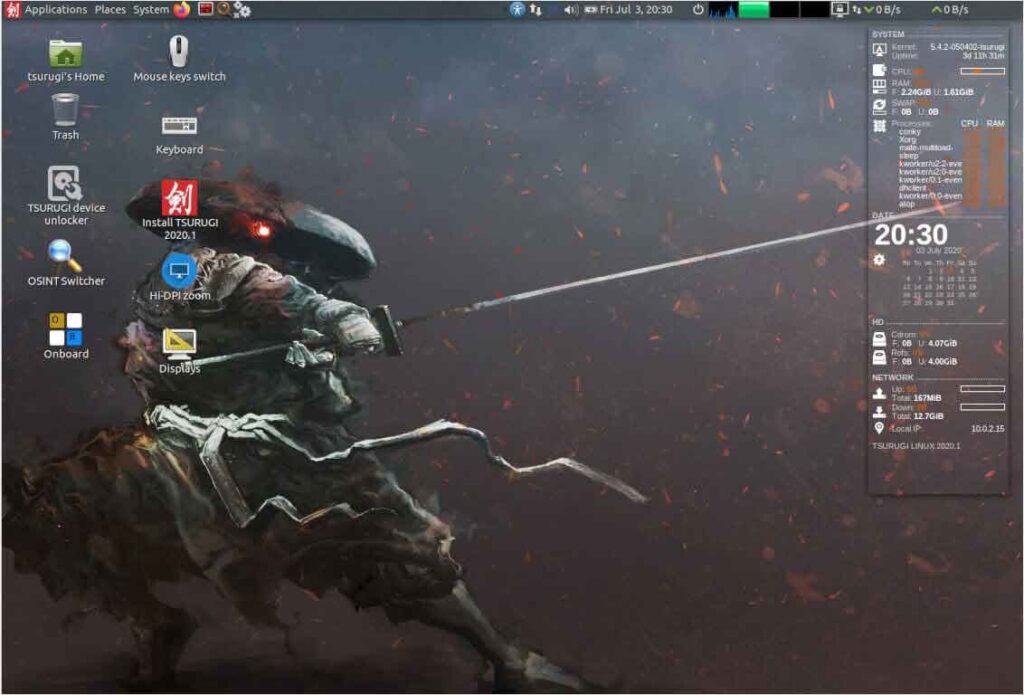
Once logged in, we see a simple GUI, carefully weighted on all sides of the widgets performance indicators of the processor, hard drives, RAM, network speed and more.
Yes, the hand of Kali creators is quite noticeable here. The abundance of pre-installed tools that are not always needed immediately catches the eye. At the same time, the system interface looks more than minimalistic and compact. But the logic of the security system is based on DEFT best practices, as well as on the web or tracking protection.
The entire basic arsenal is located in Applications → TSURUGI.
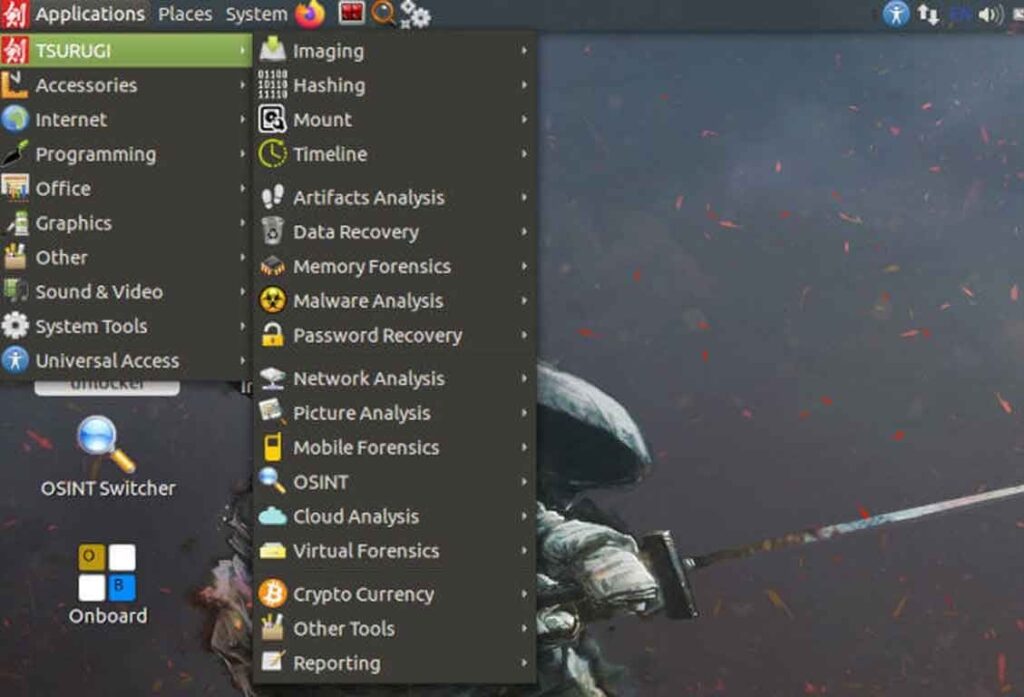
Here you can work with images, malware analysis, data recovery, and, as mentioned, a set of utilities for OSINT.
It should be kept in mind that this OS, like Kali, has no protection from hand curves. It is suitable for those who have good Linux skills and are careful and thoughtful. Just like a sharp Japanese sword should!
The extensive toolkit allows to use the system as a multitool for a wide range of tasks. Even though Tsurugi looks a bit like Kali, there are still serious differences. While some of the tools, like Kali, work incorrectly or don’t work at all, the percentage of problem tools is much smaller and you can see that someone is taking care of it.
If for some reason you don’t want to use Kali, Tsurugi will be a worthy tool in your set of top hacker operating systems. Let’s not put five stars at least because one of the authors of this review postponed the brick from the sound of the sword when starting the operating system… However, let’s not talk about sad.
Download the Tsuguri hacker operating system
Parrot
- First release: 2013
- Based on: Debian
- Platforms: x86, x64, ARM
- Graphic shell: MATE
This beautiful chaire Linux distribution is based on Debian and was developed by the Frozenbox team specifically for computer system security tests, looking for and evaluating various vulnerabilities.

What is inside? As a desktop environment, it is still the same MATE. The experience of using it is (subjectively) pleasant.
At the top, in the Application section, you will find the Anon Surf utility. One of the features of Parrot is that it pre-installed some means of anonymization, and when you select Anonsurf Start, all system traffic will be redirected through Tor. In the same section, you can use the DNS project OpenNIC – it is an invasive alternative to the top-level domain registries. Here, you can also check the current external IP by selecting the Check IP option.
The second section is Cryptography. Here you should pay attention to the GPA utility, which is a graphical interface of the GnuPG program designed to encrypt information and create electronic digital signatures. In fact, it is an alternative to PGP encryption. And if you need GPG, the zuluCrypt utility is at your fingertips – the analogue of VeraCrypt, which allows encrypting folders, partitions, flash drives, etc.
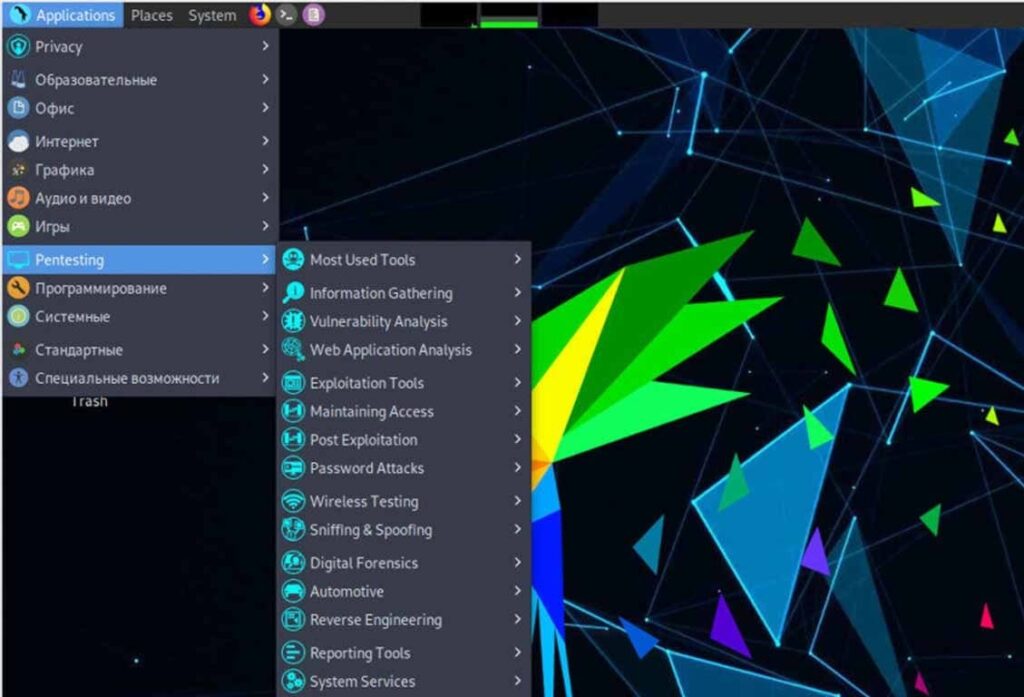
The next (and most interesting) partition is Parrot. It contains exactly those utilities for testing the security of computer systems, which made this OS in the review “Best Operating Systems for the Hacker”. We already know many of these utilities from Kali Linux but they are also unique.
For more information we would like to mention the “Internet” tab. Here we see the pre-installed Tor Browser and Electrum bitcoin wallet and the XSSer utility, a framework for detecting and exploiting XSS vulnerabilities in web applications. There is Claws Mail client, it’s a full-fledged mail client with GPG encryption support. Bonus is Ricochet IM – decentralized anonymous messenger working through Tor network.
This is probably all the features of Parrot Security OS that we would like to talk about. As you can see, Parrot OS is not only suitable for penetration tests, it can also serve as an OS for daily use by those who know why they need it.
Parrot seemed to us to be a quality and convenient hacker operating system. It’s nice to work with a system where you don’t have to fix the tools beforehand.
Download Parrot Security
BlackArch
- First release: unknown
- Based on: Arch
- Platforms: x64
- Graphical shell: none, there are several desktop managers
BlackArch is the largest distribution by volume of image. The current version takes more than 14 Gbytes! You can download, by the way, if you wish, through the torrent, and there are always a lot of seats.
Check out the friendliness of the interface: if you managed to download this monster and run it, you need to enter your login and password, which you should read about on the site in the installation instructions (this is root/backarch, if anything). The live users seem to have been forgotten.
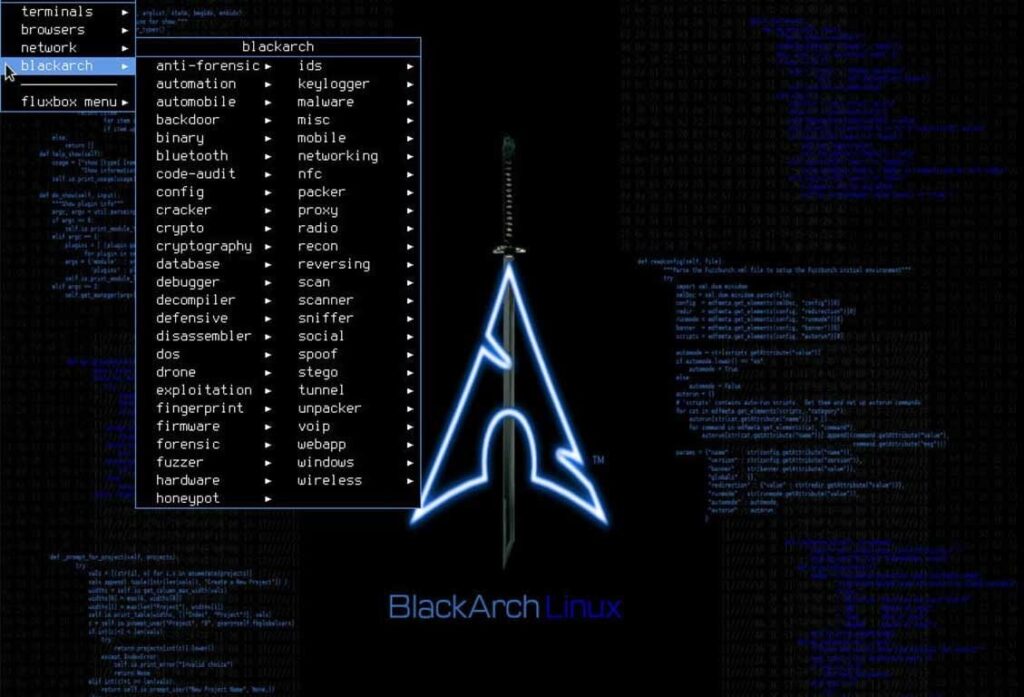
Next: after the login you can’t see any hints on the menu or anything like that. The Fluxbox is almost naked in front of us, so it can be called by right-clicking anywhere on the desktop.
All applications are conveniently categorized in the blackarch submenu of the main menu. There are 49 categories with tools for any occasion. How do you navigate the menu with a mouse, like in Windows? Oh no, in this distribution you can safely forget about the mouse. Keyboard only, hardcore only! On the other hand, since you decided to contact *nix systems and hacking, it’s foolish to count on something else.
As for the tools themselves, here are all the popular and not so popular tools for hacking, including, of course, such iconic as Metasploit and BeEF XSS. Reviewing all the tools in this truly huge set is even more hopeless than with Kali and Parrot. So I’ll go through the tops, and you can delve into reading the documentation as much as you like, if you want.
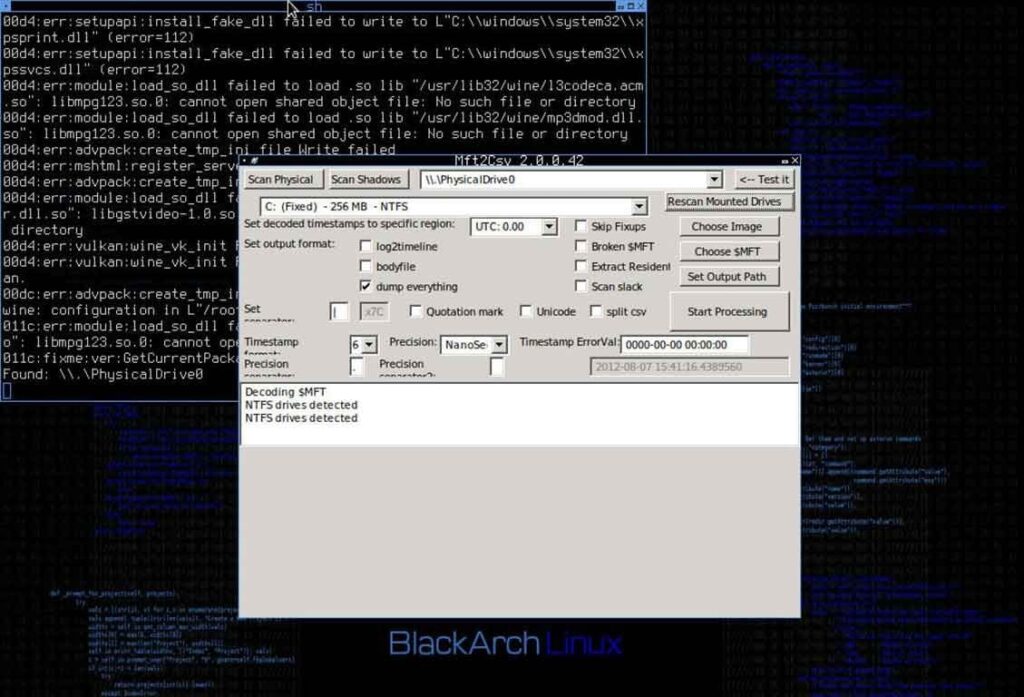
BlackArch does not hesitate to use Wine to run some “non-native” applications. As an example, mft2csv (in the screenshot above) will parse the MFT file system of NTFS for further analysis. Java (OpenJDK 14.0.1) is also available.
MSF is also available.
MSF is also in place.
The terminal, as well as the whole graphic shell of the system, looks depressing, but the software versions are up-to-date. On the one hand, it seems that they wanted to do as in a movie about hackers, on the other – the system is still quite usable, although it requires serious skills.
In general, if you are not ready to sneak through a minefield of configs, arguments when running the software, googlenya for every sneeze and other delights of this multi-talent – look in the direction of Kali and Parrot, there is something you can do without a desktop guide. For beginners BlackArch is more than unfriendly. And, clearly, do not put it as the main one.
Download BlackArch from the official website
BackBox
- First release: 2010
- Based on: Ubuntu
- Platforms: x64
- Graphical front-end: Xfce
And at the end of the last distributive for breaking and entering, standing a mansion from the others. BackBox does not pretend to be the best hacker multitool, but it is best suited for everyday use. The graphical shell here is Xfce, which minimizes system resources consumption. There are two options available for download from the site – ISO and Torrent. There is no image for virtual machines.
BackBox is based on Ubuntu (more precisely, Xubuntu), which makes it convenient to use as a home operating system, in addition to Ubuntu available a lot of documentation and forums with answers to common questions. There are no kernel tweets here, so no machinations will spoil anything. These features make this distro a great choice for a beginner pentester.
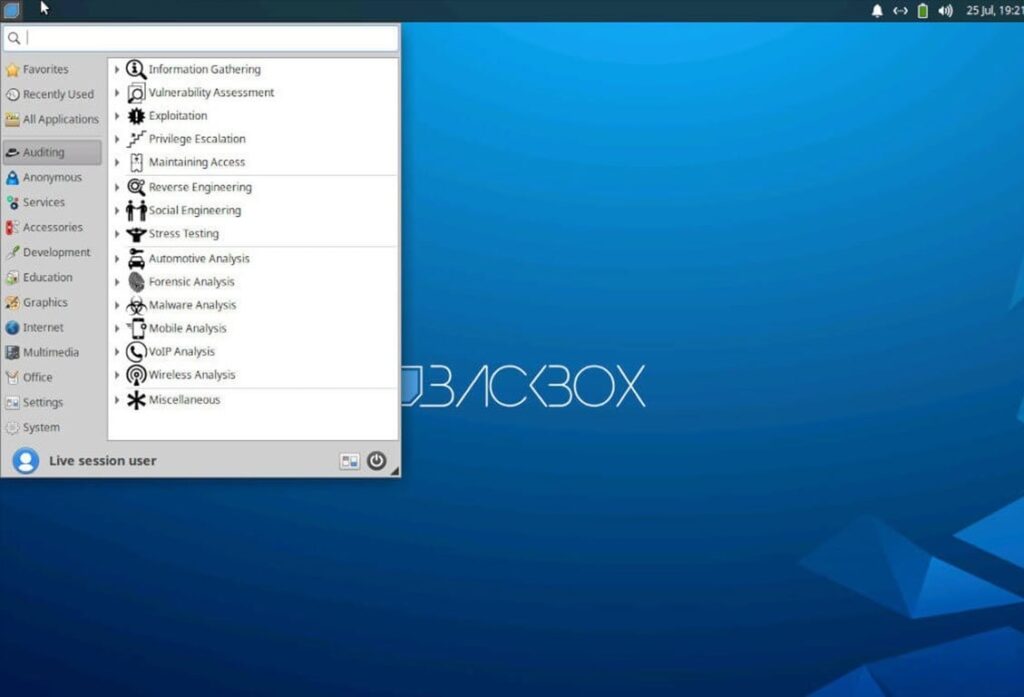
There are not many tools from the box, only about 200 pieces, but for the first steps in information security is enough. Otherwise, BackBox is just an Xubuntu with all its bug features and functions.
An important plus that I can’t ignore is that all the tools are conveniently grouped in a menu. Even if you don’t know any tools, like hacking into WiFi, you can easily find them.
There’s nothing more to say, just use them in good health.
Download BackBox
Distribution table for a hacker


















