Cloud Security Challenges
1 July 2020I recently sat down for a couch talk with our product marketing manager Yitzy Tannenbaum. We wanted to share my experience of working with hundreds of companies worldwide and in different industries, and talk about how their security approaches can be compared and contrasted at the same time. Together we discussed the changes I see in corporate security and how different organizations manage security differently in their complex network environments. I would like to give some excerpts from our conversation here.
Table of Contents
- Cloud computing touches everything
- That makes security more complex
- Get control of security
- Security rules overload
- Transition to continuous compliance
- Accelerate changes
- Simulated phishing campaigns – goals, forms and their problems
- Digitization and cyber security – How to Make Digital World Secure
- Create Your Own Python Keylogger Which Emails About Every Keystroke.
- Top 6 reasons why PMP certification is worth it !.
Cloud computing touches everything
Every single customer I work with has decided to move parts of their IT infrastructure to the cloud in one way or another. As a result, some business applications are now being moved from the traditional data center to the cloud and software-defined networks (SDN). The traditional on-premise network is gradually being converted to cloud or hybrid implementations. However, these hybrid environments require complex sets of firewall policies, which increase the need for security solutions to manage these network rules.
That makes security more complex
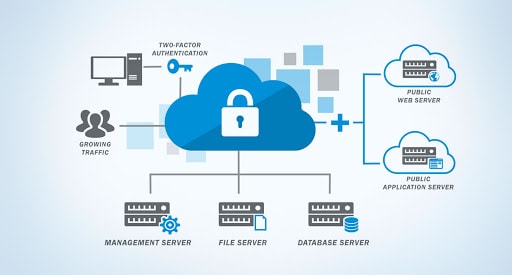
Common cloud providers, such as Amazon Web Services (AWS) and Microsoft Azure, offer integrated security controls at little or no cost. To a certain extent, these are even very effective. However, we can see that companies are also introducing classic third-party firewall providers, usually at the virtual private cloud (VPC) or VNet level, in order to achieve a higher level of filtering and control. That’s what these firewall providers are good at – they enable the greater level of control required to segment larger networks or VPCs within the hybrid or cloud environment.
This means that companies work with a combination of hybrid, cloud and on-premise security controls every day, managed by very different people with very different priorities – and traditionally at very different speeds. As we know, the cloud is very dynamic in its structure – keyword: enormous scaling – and allows high speeds with many connections – a breakneck speed compared to traditional hub-and-spoke models.
Get control of security
For this reason, organizations are beginning to change their concepts. Many of our customers have now deployed special cloud security teams, while others have passed security control sets on to DevOps personnel – the latter are actually responsible for introducing new code into the cloud. However, this can entail the risk of a ‘wild west scenario’: Suddenly, departments that are very interested in connectivity to the cloud – to enable the use of their applications – have to take care of security controls themselves.
The risk is obvious: DevOps personnel may not have a security background and are therefore less inclined to manage security in the cloud in a manner that is consistent with general corporate governance. This is why traditional security groups are so keen to gain insight into the cloud to regain control of network traffic.
A big challenge for companies lies in the area of network and security and consists in bringing these isolated processes together. Then the staff in the cloud and at DevOps can make changes in the cloud very quickly by directly addressing the APIs and the cloud providers.
However, the connectivity that must exist in the on-premise environment to ensure that all applications work is still done through cumbersome, manual firewall changes. This can easily lead to errors that span local and cloud environments – in our May 2019 survey on security challenges in the cloud, 42.5 percent of respondents experienced a network or application failure. The main cause was an operational or human error in the management of security devices. For this reason, companies are increasingly looking for automated security solutions that provide a comprehensive overview of the environment and complete control from a single platform.
Organizations must have the ability to see cloud, on-premise, and SDN in one place and see connectivity for key applications in all of these environments at a glance. You cannot tediously handle different processes and technologies.
Security rules overload
During our conversation, Yitzy Tannenbaum and I discussed the challenge for organizations that have to deal with a business-critical mistake. It is clear that the priority is to get the application up and running as quickly as possible. However, this means that there is a temptation to redirect the data traffic or to change a security rule quickly without optimizing the existing rules themselves.
When I go to a large company and look at the largest data center there, for example, there are very often firewalls that have been in operation for years. They usually have an organic structure and have undergone several moves in the data center or from firewall to firewall. A massive block of security rules has built up over the years.
Large companies in particular therefore have a huge inventory of security rules to manage. Typically, when we analyze a new customer’s security infrastructure, we find that 50 percent – or even more – of their security policies could be revised or optimized. Due to a company’s highly dynamic network environment, this cleanup must be done earlier than later.
Transition to continuous compliance
Another effect of the increasingly dynamic, fast-paced network landscape is the need to recognize that companies can no longer understand compliance checks as a secondary matter, which is carried out once a year, like an exercise. Auditors are increasingly understanding this and are therefore looking for ways to maintain compliance. You are looking for auditing solutions that also issue a warning if there is a change in the network that affects compliance.
This is where security automations come in, which take care of the administration and change of security policies and can meet these requirements. The new network landscape also has the effect of giving application owners a very clear idea of the level of risk that their applications pose to the corporate environment. This enables you to take more responsibility for the business impact of the changes you want and to be able to examine them more closely. This does not mean that application owners are suddenly responsible for the security of their applications – they get a better sense of how a particular application affects the company’s threats.
Accelerate changes
Our discussion brought us to the subject of ‘Zero-Touch Security Automation’. In line with cleaning up the security rules in a typical network and focusing on continuous compliance, zero-touch security is essential. It ensures that companies can remain secure and agile as their networks become more complex and change quickly.
All of this falls under the long-established security principle of least privileged access. The idea is actually not new, because it only says that only applications that really need to talk to each other should be connected via the network. However, when networks grow and become more complex, and change organically over time, this principle often falls by the wayside – and with it control by IT departments.
To regain this, companies must be able to control all connections within their IT environment. Security automation helps enormously, which relieves the employees of many manual processes, which are difficult to manage, so that they can concentrate on the really important tasks of securing the company.
Join DICC now for cyber security course in Delhi.
















